- This Will Prevent The Passphrase Prompt From Appearing And Set The Key-pair To Be Stored In Plaintext (which Of Course Carries All The Disadvantage...
- Ssh-keygen-g3 Options
- Ssh Keygen Generate
- Ssh-keygen-g3 Command Not Found
SSH Frequently Asked Questions
How do I get publickey user authentication to work?
The first thing to understand is that there is no one answer to thisquestion. The SSH protocol only specifies the syntax and semantics ofmessages passed on the network ('over the wire') between an SSH client andserver. It says nothing at all about host-dependent issues, such as howpublic keys may be encoded in files, or how to indicate that the holder ofa particular public key is authorized to log into a particular account.As a result, these issues vary from one implementation to another — andmay get especially interesting when connecting from one implementation toanother.
Ssh-keygen-g3 -v Generating 2048-bit rsa key pair 3 o.oOo.oOo.oO Key generated. Copy link 42wim commented Nov 18, 2018. Got the same issue on trying to connect.
First, let's understand how publickey user authentication works ingeneral. In the SSH protocol, a client may make two different requestswith regard to publickey authentication. The first is a probe request: itsimply asks whether a given public key is authorized to access a givenaccount. The second is an actual authentication attempt: it includes adigital signature generated by the client, which should convince theserver that the client possesses the private component of the given publickey. The first form exists because generating a digital signature is acomputationally expensive operation, so if a client has several differentkeys available, it is better to test them first and only attemptauthentication for those keys which are authorized for login on theserver.
From this description, we can see that the client needs the privatekey, while the server needs the corresponding public key. While thepublic and private keys are usually written to a pair of files whengenerating a key, these files need not always be copied as a pairtogether, and in fact often should not be. For instance, there is no needto have a copy of your private key on a remote host, and you may not wantit exposed there if that host is less trusted than the local one.
- Login via ssh resp. Filetransfer via scp is also possible without having to enter a password. Authentification is done via a public/private key pair. The following steps have to be accomplished: (system1 is the machine from which you logon to the target system system2) System1 ssh-keygen Generating public/private rsa key pair.
- Ssh-keygen may be used to generate groups for the Diffie-Hellman Group Exchange (DH-GEX) protocol. Generating these groups is a two-step process: first, candidate primes are generated using a fast, but memory intensive process. These candidate primes are then tested for.
- By default, ssh-keygen-g3 creates a 2048-bit DSA key pair. RSA keys can be generated by specifying the -t option with ssh-keygen-g3. Key length can be specified with the -b option. For automated jobs, the key can be generated without a passphrase with the -P option, for example: $ ssh-keygen-g3 -t rsa -b 1536 -P.
- Dec 14, 2020 Run ssh-keygen-g3 to generate the host key, for example: This will generate a 2048-bit RSA key pair without a passphrase and store it under /opt/tectia/etc. For more information on the key generation options, see the ssh-keygen-g3 man page. Restart the server as instructed in Section Restarting sshd2. Contents Index.
Another point about key pairs: from following 'recipes' for setting uppublickey authentication, people sometimes get the idea that they mustrepeat this entire process for every client/host pair — that is, that youneed a separate key pair for each remote host. While you can dothat, it's not necessary; a single key may be authorized to log into manydifferent hosts.

OpenSSH client and server
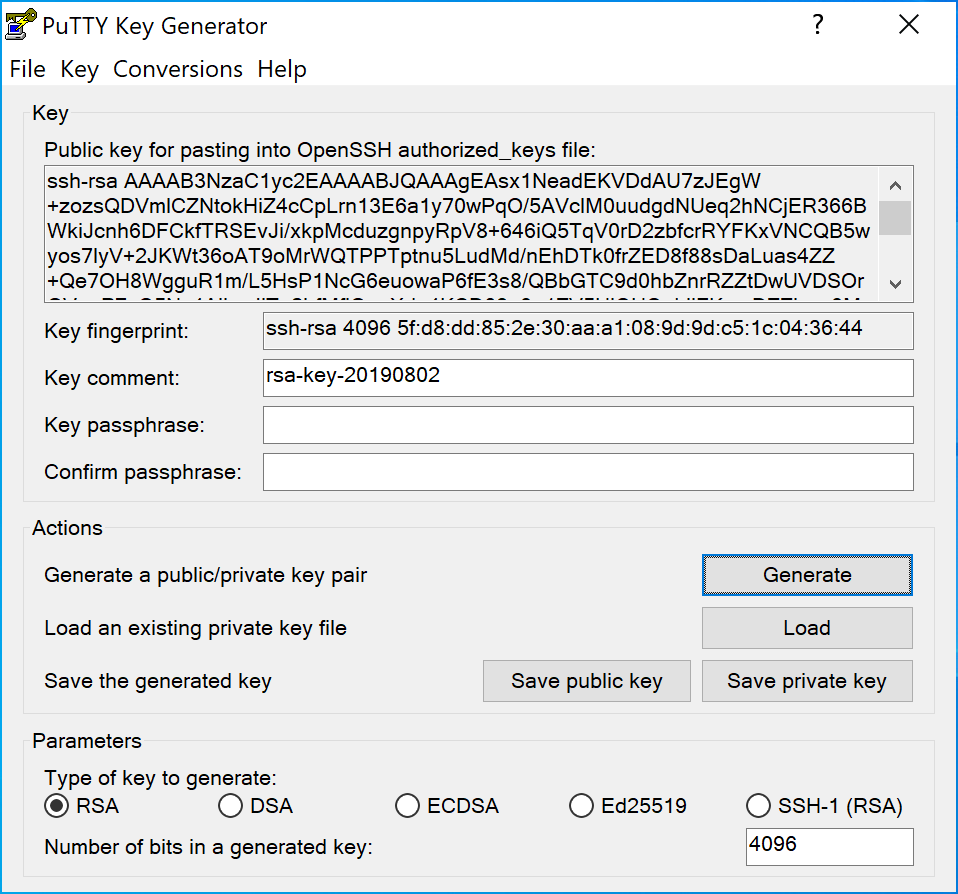
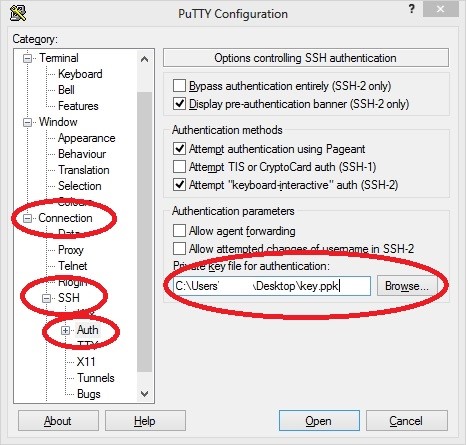
Let's take the most common case: the client and server SSH software areboth OpenSSH. To generate a key pair on the client:
This generates a new RSA private key and places it in the defaultlocation, ~/.ssh/id_rsa. ssh-keygen saves the corresponding public key in~/.ssh/id_rsa.pub; you can recover this at any time from the private keywith ssh-keygen -y -f private-key-file. OpenSSH trieskeys in this and the other default location (~/.ssh/id_dsa) automaticallyduring client authentication. You can change this using the IdentityFileoption in ~/.ssh/config.
SSH protects your private key by encrypting it with the passphrase yousupply; you will need to supply the passphrase whenever the key needs tobe loaded from that file. You may be tempted to leave it blank to makethings easier; don't do it. There is a tool that gives the sameconvenience without completely compromising your key: ssh-agent. See this discussion for more details.
Now that you have a key, you need to authorize it to log into your accounton the remote host, let's say account pat on the hostremote. When asked to log into the account pat, the OpenSSHserver (sshd) on remote looks in a particular file for a list ofpublic keys authorized for the account:~pat/.ssh/authorized_keys. So, in order to authorize your newkey, you can copy id_rsa.pub to remote (e.g. using scp), and appendits contents to the authorized_keys file. Note that each public key isrepresented on a single line, usually quite long, like this:
If you use a text editor, take care that it doesn't break the lines inthis file. Once you have added the key to authorized_keys, there is noneed to keep the id_rsa.pub file around. Also note that there isnever a need to copy the private key file (id_rsa) to the serverjust for authentication to work; in fact, you would not generally want to.If you need further authentication from that host, consider usingssh-agent together with agent forwarding to get this effect.
File and Directory Permissions
Here's an issue that frequently trips people up: by default, sshd hasrequirements for the permissions on the authorized_keys file, as well asits containing directory ~/.ssh, and the home directory.Specifically, none of these may be writable by any uid except the owner orroot. That means the most permissive modes you can have here are:

The reason for caring about the directory permissions, is that it doesn'tdo much good to protect the authorized_keys file, if someone else cansimply delete it and create a new one (by modifying the containingdirectories).
Try it!
Once everything is in place, try ssh pat@remoteThis Will Prevent The Passphrase Prompt From Appearing And Set The Key-pair To Be Stored In Plaintext (which Of Course Carries All The Disadvantage...
and see whathappens. You can omit the 'pat@' part if the local and remote accountnames are both the same. OpenSSH should prompt for your key passphrase,then log you into the remote host. If you have trouble, see our debugging hints. The ssh -v outputfrom a successful authentication will look like:Server Host Keys
One source of occasional confusion, is that two different kinds ofauthentication take place with each SSH connection: server, and client.Here we are dealing with client (or user) authentication, but theclient also authenticates the server first, and this usually also entailssome keys called the server's hostkeys. In client authenticationwe have seen that the private key is on the client and the public key onthe server. With server authentication, then, the roles are reversed: theserver's private hostkeys are on the server (usually in /etc/ssh/), andthe user needs copies of the public hostkeys in order to authenticate theserver; these are kept in ~/.ssh/known_hosts. Be careful to distinguishbetween these: the hostkeys and known_hosts file have nothing to do withpublickey client authentication..
Tectia SSH (ssh.com)
SSH Communications Security (ssh.com) sells a suite of SSH software calledTectia. The concepts here are the same; only the detailsdiffer, such as file names and formats. Tectia also keeps key pairs infoo/foo.pub files, in the directory ~/.ssh2, and you can create them withthe Tectia version of ssh-keygen. On the server, there is a file~/.ssh2/authorization, which contains lines referring to authorized publickeys in separate files, rather than the keys themselves. E.g.:
Tectia has the same default requirements on server file permissions as thosementioned above for OpenSSH.
Ssh-keygen-g3 Options
Mixing Implementations
Ssh Keygen Generate
Since the file formats used by OpenSSH and Tectia (and other SSH software)may differ, you usually have to convert key files from one format toanother when connecting between implementations. For example:Ssh-keygen-g3 Command Not Found
- To convert a Tectia public key for use on an OpenSSH server:
- OpenSSH: ssh-keygen -i -f [filename].
- To convert an OpenSSH public key for use on a Tectia server:
- OpenSSH: ssh-keygen -e -f [filename].
- Tectia: ssh-keygen --import-public-key [infile] [outfile]
- To convert a Tectia private key for use by an OpenSSH client:
- OpenSSH: ssh-keygen -i -f [filename] (Tectia key must be unencrypted)
- To convert an OpenSSH private key for use by a Tectia client:
- Tectia: ssh-keygen --import-private-key [infile] [outfile] (OpenSSH key must be unencrypted)